New Zealand
Deadline approaches for reporting on New Zealand’s Minimum Cyber Security Standards

There is less than one month to go until the deadline for New Zealand’s core Government agencies to report their standings against the nation's new Minimum Cyber Security Standards.
The Standards were released in 2025 with the aim of driving sector-wide uplift against foundational cyber security practices, similar in nature to Australia’s Essential Eight or the UK’s Cyber Essentials.
Originally targeted at GCISO-mandated agencies as a pathway to lifting and benchmarking security practices in alignment with the country’s Information Security Manual (NZISM) and Protective Security Requirements, non-mandated agencies were also encouraged to adopt and apply the Standards.
The Standards were based on an assessment of the most likely vectors for cyber attack and historic incidents responded to with stated aims being to:
· Establish clear foundational controls mapped to New Zealand’s own Cyber Security Framework
· Help agencies understand, benchmark and improve practices against a maturity model
· Generate system insights through mandated agency reporting and allow better oversight of cyber risk and maturity
Intended enforcement of the cyber security standards was part of the country's recently updated Cyber Security Strategy for 2026 – 2030 and shows the direction of travel.
Understanding New Zealand's cyber security mandates
NCSC-NZ’s Cyber Security Framework provides a basis for the development of the initial set of Standards with a simple visual mapping of Standards to the 5 top level Functions (Guide & Govern, Identify & Understand, Prevent & Protect, Detect & Contain, Respond & Recover):
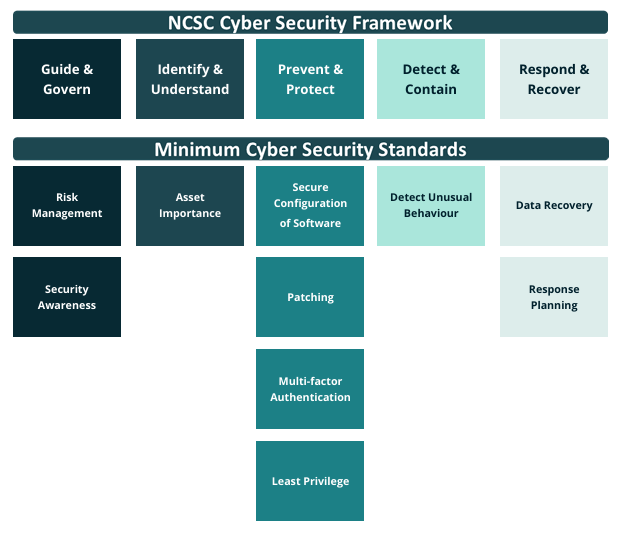
The ten minimum Standards include:
- Risk Management
- Security Awareness
- Asset Importance
- Secure Configuration of Software
- Patching
- Multi-factor Authentication
- Least Privilege
- Detect Unusual Behaviour
- Data Recovery
- Response Planning
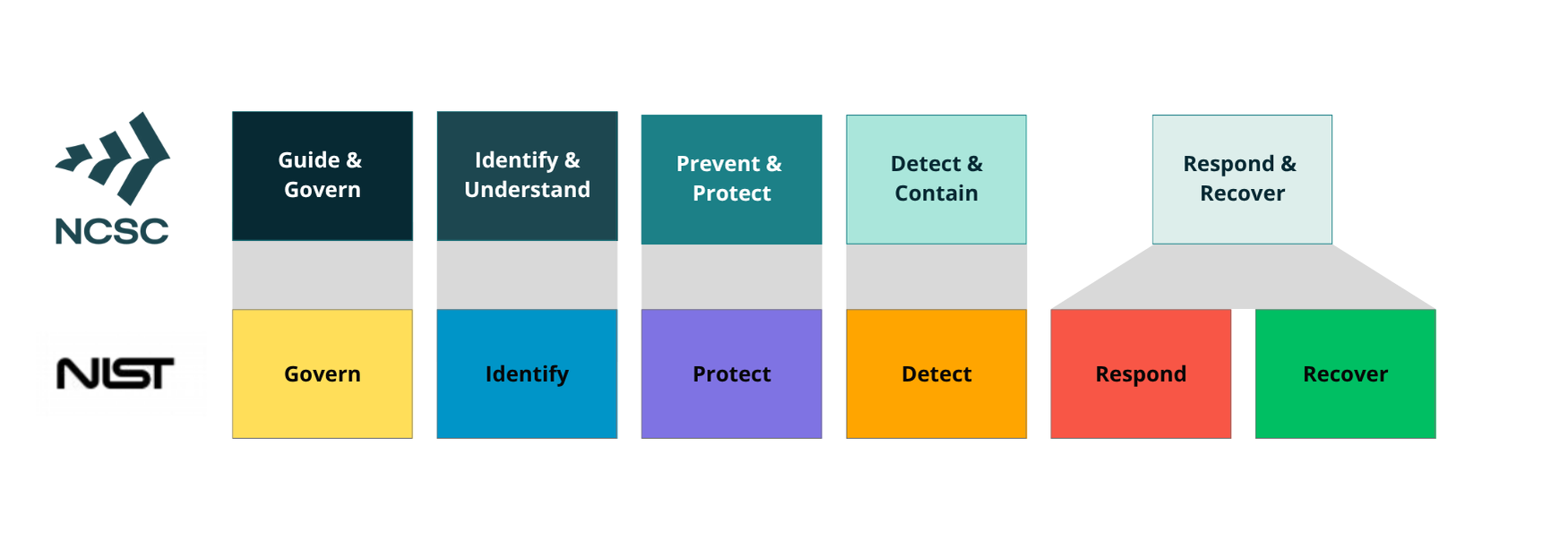
The NZ Framework, released in 2024, remains closely aligned with the United States approach but provides less detail when you dive into the Categories and Sub-catgeories.
In New Zealand, the Protective Security Requirements (PSR) has been the Government’s best practice security framework for security governance across personnel, information, and physical security domains since 2014.
Under the PSR, every public service department needs to have a cyber security framework and thus the NZ adaptation can be referenced as a localised and less stringent approach to control selection.
Under the Framework, security objectives and target outcomes are the basis for guidance, the Standards now slotting in below the Functions and linking back to the prescriptive NZISM.
Reporting against the 20 domain PSR is well established with public service agency data allowing the New Zealand Government to better understand its overall protective security capability.
Agencies set out in Schedule 2 of the Public Service Act 2020 - plus the New Zealand Defence Force, New Zealand Police, New Zealand Security Intelligence Service and Parliamentary Counsel Office fall into scope.
There is no legal requirement for the hundreds of Crown Agents, Autonomous Crown Entities and Independent Crown Entities to adopt the PSR, however it is encouraged as good practice and considered a safe approach locally.
Scoring maturity against MCSS
Along with the 10 Standards, NCSC-NZ provides a Cyber Security Capability Maturity Model (CS-CMM).
Each maturity level - from CS-CMM 1 to CS-CMM 4 - has a number of specific requirements where agencies can assess progress and maturity through a set of measures with associated guidance outlining the steps for uplift through the Maturity Model and plotting resulting areas requiring attention.
The minimum maturity level for GCISO-mandated agencies has been set at CMM-2 - Planned & Tracked but with the caveat that a risk assessment to determine organisational risk profile and specific threats may require a higher level of maturity. Each agency after all, does not undertake the same type of work and critically differs.
Agencies have submitted an annual self-assessment against the twenty PSR domains for many years. What the MCSS now brings is additional reporting requirements for Information and Cyber Security specifics.
The reporting period for the first ever assessment against the Minimum Cyber Security Standards runs from 1 November 2025 to 30 April 2026, coinciding with the PSR assurance round.
A new tab in the PSR Self-Assessment Tool sets out questions and has a built-in analysis capability, which analyses the inputted results and provides a consolidated view of an organisation’s maturity based on the self-reported data. Spider graph or radar chart lovers will be able to see their standing immediately:
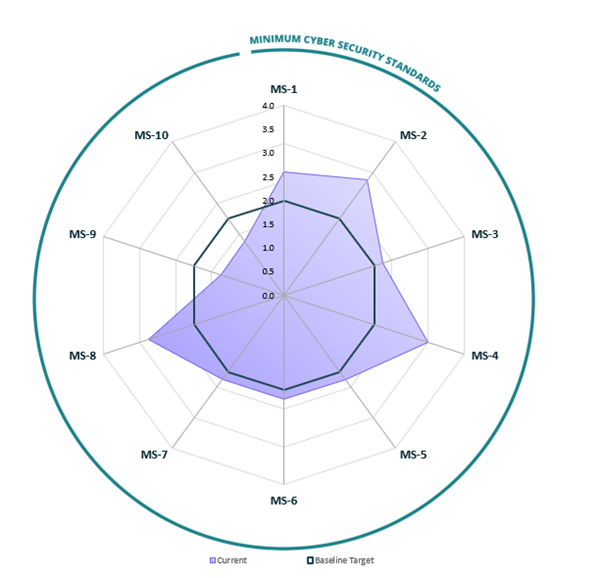
With weeks to go, NCSC-NZ will soon have more insights on compliance with the cyber security minimum baseline expected.
Reporting of PSR results has never - for good reason - been made public but perhaps there is a chance in future to surface some aggregate findings over the nation's attack surface and key gaps to address, if only to support future investment in the new national strategy.
In Australia, both the Audit Office of New South Wales and Western Australia's State Government have provided high level insights into information and cyber security audit findings and these have been used to add urgency to programmes.
At Overcyte, we've made the MCSS available in the platform for any organisation to assess their maturity against a local baseline.







.png)

