Regulation
New Japanese Cybersecurity Strategy will establish a unified standard for security at operators of critical infrastructure

Japanese Prime Minister Sanae Takaichi's government plans to adopt a new national cybersecurity strategy next month that calls for increased effort to address foreign threats such as election interference by China, Russia and North Korea, AI weaponisation and misinformation campaigns.
The strategy announcement called for "defence and deterrence with the state at the core" following the enactment of a law to introduce active cyberdefense to protect Japanese businesses and infrastructure.
In May 2025, the country passed the Active Cyber Defense (ACD) Act to enable preemptive cyber threat disruption - including attacker infrastructure takedowns - under a new regime to be live by 2027.
Setting out CNI security requirements
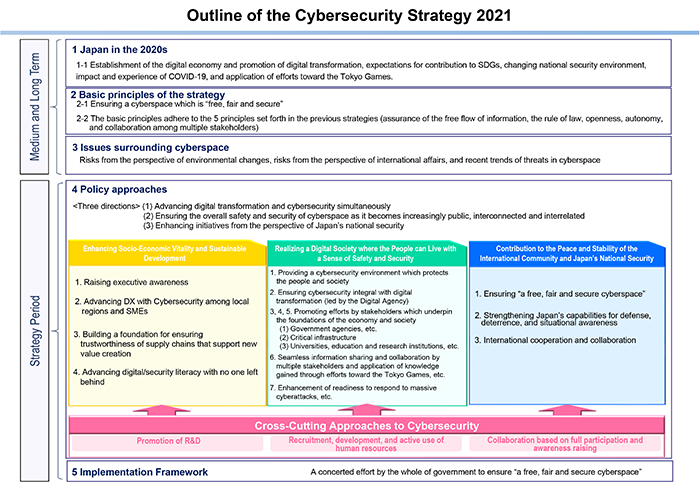
Japan's most recent cyber strategy was published in 2021 with five key principles - following a series of high-profile incidents and breaches, there is growing concern about protecting key systems and the new strategy will kick things up a gear in response.
Under the new strategy, in 2026 the government will launch a unified standard for cybersecurity measures to apply to all operators of critical infrastructure. It has also suggested expanding the scope of critical infrastructure protection to ensure all key assets are adequately protected.
Since 2005, the Cybersecurity Policy for Critical Infrastructure Protection has been set as a common shared action plan between the government and CI operators. A new edition was published in 2022 and identifies 14 sectors as critical infrastructure with stakeholders expected to undertake the five measures below:
- Enhancement of Incident Response Capability
- Maintenance and Promotion of the Safety Principles
- Enhancement of Information Sharing System
- Utilization of Risk Management
- Enhancement of the Basis for CIP
New cybersecurity requirements for the semiconductor industry were established earlier this year and in October draft Guidelines on the Roles Expected of Cyber Infrastructure Providers were set out to bring the country in line with Secure By Design efforts globally.
The guidelines define business entities that develop, supply, and operate software - dubbed suppliers of information systems which includes cloud services - as “cyber infrastructure providers" that must meet new requirements.
Software includes embedded software and firmware provided as part of hardware products such as IT/OT/IoT devices, and software provided as components of systems and services.

The Ministry of Economy, Trade and Industry (METI) and National Cybersecurity Office (NCO) are working together to update numerous standards and guidelines across the Japanese economy, with the foundational Basic Act on Cybersecurity being updated in July 2025 to prescribe new obligations to businesses "to make reasonable efforts to provide necessary support for users’ endeavors to ensure cybersecurity."
2026 will bring further cyber regulation
The Active Cyber Defense Law, which will become operational in 2027, has new rules on cyber incident reporting designed to enhance oversight and visbility of attacks.
The new rules will apply to approximately 250 entities across finance, telecommunications, transportation, energy, and other industries vital to national security and public welfare.
Japan has recorded a 340% increase in sophisticated cyber-attacks over the past 18 months so there may yet be further tightening of security regulations to implement via the updated national strategy.
Overcyte will be keeping up to speed with regulatory developments in Japan and watching to see how new CNI requirements align with security control frameworks for OT/ICS environments around the world.








.png)

