Regulation
New Zealand reboots national cybersecurity efforts after a series of major incidents

The National Security and Resilience Group at New Zealand's Department of the Prime Minister and Cabinet (DPMC) has issued two long awaited publications following a recent series of security breaches.
On Friday 27th February, the agency published the fourth national cyber security strategy for 2026-2030, the first update since the last Government roadmap was issued in 2019.
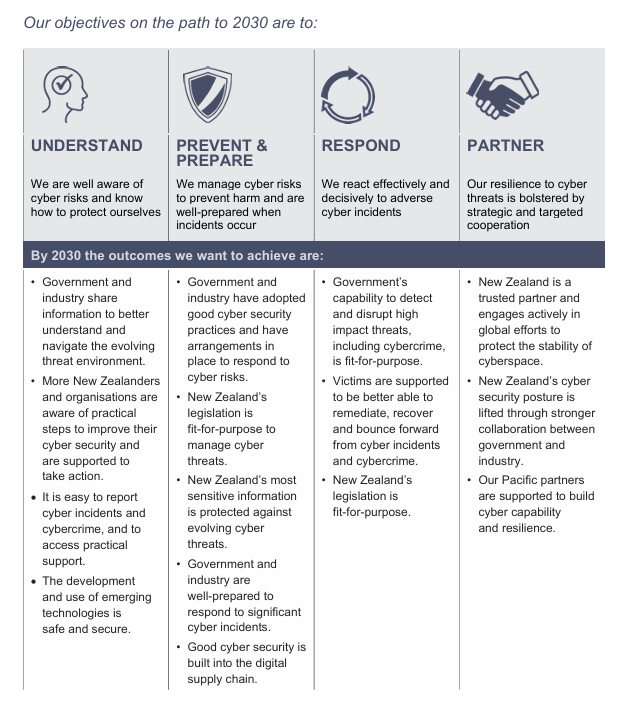
This latest strategy is designed to "foster collaboration between government, industry and community so that we can all protect our digital spaces," and sets out four key objectives:
- Understand: ensuring our people are well aware of cyber risks and know how to protect themselves.
- Prevent and prepare: Managing cyber risk to prevent harm and are well-prepared for incidents that occur.
- Respond: Reacting effectively and decisively to adverse cyber incidents.
- Partner: Ensuring our resilience to cyber threats is bolstered by strategic and targeted cooperation.
The document is signed by Rt Hon Christopher Luxon, Minister for National Security and Intelligence and the country's current Prime Minister.
At only 15 pages, the document is surprisingly brief given a seven-year gestation period and it's not until page 10 that the rubber hits the road with more details on what outcomes the Government is targeting:
A cybersecurity vision for New Zealand
The vision established is for "A New Zealand that embraces cyber security to enable innovation, drive a prosperous economy and protect our digital way of life."
A supporting Action Plan for 2026–2027 details fifteen immediate steps to achieve the strategy’s objectives with a commitment to deliver the overall four-year strategy in phases by reviewing progress and refreshing the Action Plan regularly.
The four objectives - Understand, Prevent and prepare, Respond, and Partner - set out the context for the current threat landscape in New Zealand with an estimated $1.6bn in direct financial losses attributed to online threats annually in the country.
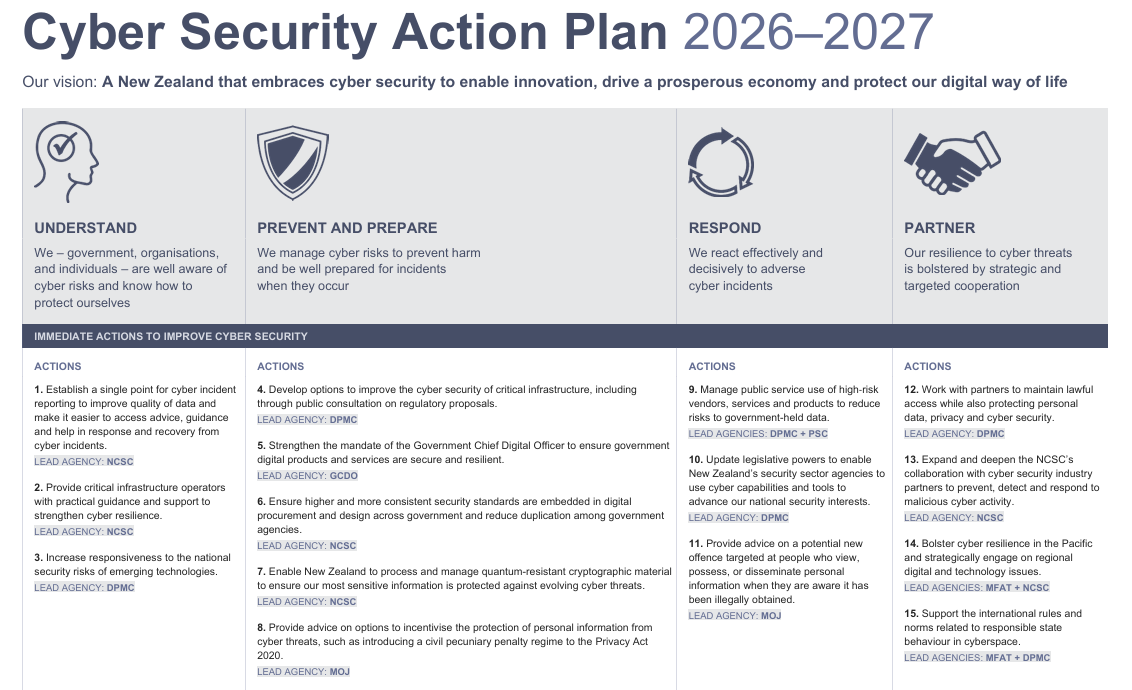
A one-page summary of the Action Plan highlights the key responsibilities that will be shared across the National Cyber Security Centre, DPMC, and the Ministries of Justice and Foreign Affairs, the latter covering off boosting cyber security capabilities in the Pacific region and aligning to international rules.
Security incidents are growing in NZ
"New Zealand has been behind other countries for many years on this. Our government is now working very rapidly to keep up and this has been discussed in the highest levels of government"
Associate Health Minister David Seymour
Protecting New Zealanders and New Zealand businesses against cyber threats is becoming a growing concern for the country.
2026 kicked off with a major incident over the traditional long summer break after the Manage My Health data breach.
Hackers got access to personal health data being processed and stored in the popular patient portal Manage My Health. The result has been described as one of the biggest privacy breaches in New Zealand history and the Government has since ordered a review into the events with more than 100,000 Kiwis thought to have been impacted.
And just last week, patient data was found to have been changed in a second major NZ health app, MediMap. Some live patients were labelled as “dead” and other names replaced with those of politicians and the American Charlie Kirk.
On 24th February, Prime Minister Luxon told reporters that "we need to strengthen our cybersecurity laws here in New Zealand and also make sure that we're not laid back." On that basis, the publication of the new strategy couldn't have come at a better time.
MediMap has sought to use the trusty court injuction option to stop sharing of stolen data. And Health NZ’s former chair Rob Campbell has told media the reason for the series of incidents impacting the health sector is down to a lack of investment: "[Cyber security is] expensive, it can be complex, it’s not headline-grabbing stuff so it’s the sort of thing that people do put off.”
Updating New Zealand Critical Infrastructure sectors
Whilst the impact of these two recent cyber security incidents are unlikely to reach the sheer scale of the now £7bn cost being paid by the UK's Ministry of Defence, human error and offshore hackers continue to impact personal information security.
Kiwi survivors of abuse in care were recently affected by an accidental data breach after information was insecurely shared by email. And an NZ law firm is investigating a cyber-attack and potential client data leak
At the other end of the cyber attack spectrum, concerns continue to increase around securing critical national infrastructure. New Zealand introduced Minimum Cyber Security Standards for Government Agencies in 2025. But this scheme only targets investment and verifies security measures in a tiny subset of the nation's key indsutries.
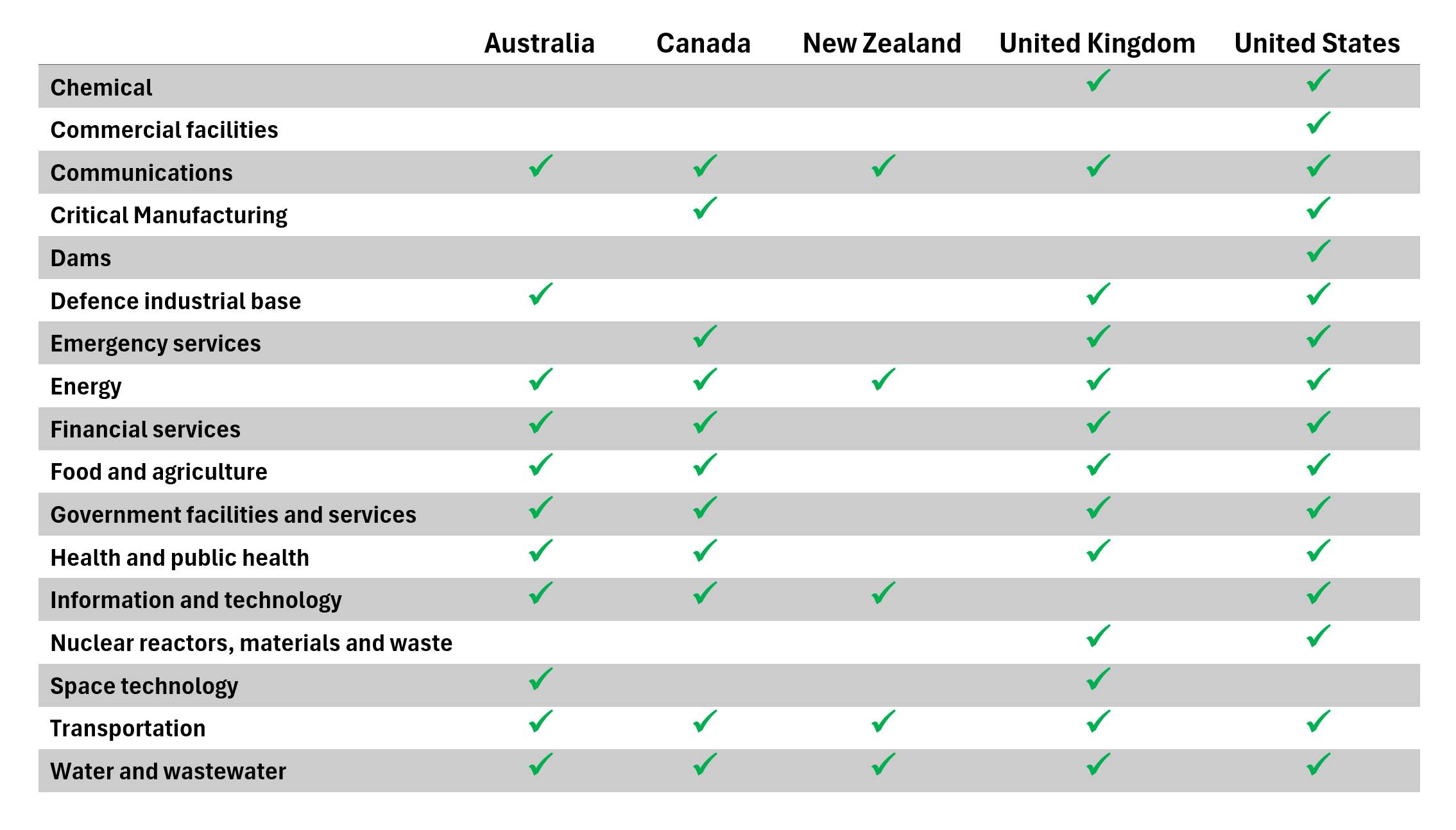
Whilst other nations have charged ahead with efforts to regulate the security of critical sectors, New Zealand has maintained a passive, voluntary approach to requiring industry investment into mitigating known cyber threats.
In 2018, Australia implemented its primary critical infrastructure security legislation, the Security of Critical Infrastructure Act 2018 (SOCI Act) and has iterated the legislation several times. Protecting Australia’s energy sector with the AESCSF has been regarded as a successful path for defending energy operators.
Comparing the security frameworks in the so-called 'Critical Five' countries shows NZ remains significantly behind other nations when it comes to CNI cyber security legislation and mandated security requirements.
Efforts to update the 2002-era Civil Defence Emergency Management Act first kicked off almost three years ago in 2023 with the Critical Infrastructure Phase 1 Consultation. Whilst many CNI operators responded, there had been no public sign of activity since January 2024.
That all changed on Friday with a new Critical Infrastructure consultation offering from the Department of the Prime Minister and Cabinet (DPMC). The consultation period runs from 27 February to 11.59pm on 19 April 2026 and seeks feedback on two key questions:
- What are the essential infrastructure services most critical to our economy and communities that they should be safeguard against harm?
- What should the depth of the cyber defences of these infrastructure services be?
Measures are designed to deliver three outcomes:- an improved understanding of threats and vulnerabilities by critical infrastructure entities and government
- a minimum level of cyber risk management by all critical infrastructure entities
- effective management of cyber threats impacting national security by critical infrastructure entities

A new approach to cyber security for NZ CNI
"Cyber risks are generally not well understood or collectively managed to a consistent level across New Zealand’s critical infrastructure system."
Rt Hon Christopher Luxon Minister for National Security and Intelligence, PM
Described as "an invitation to shape a future in which New Zealand and the services that our people depend on every day stand cyber resilient amid the global challenges of the digital age," the discussion document provides detail on the range of new sectors that would fall into the scope of new regulatory security requirements.
The reach of new minimum-security baselines would be far ranging, covering communications and data services, defence, energy, financial services, health, transport and water sectors.
There are also proposed new enforcement tools to drive compliance across operators. The critical infrastructure regulator(s) would have access to:
- compliance notices directing a breach be fixed within a specified time period
- legally binding agreements (enforceable undertakings) between the regulator and a non-compliant party that the regulator would not prosecute or apply a penalty if the non-compliant party agrees to certain actions
- non-criminal monetary penalties imposed by the courts
- criminal prosecution.
For a minor breach, fines would be limited to $50,000 - a critical breach where a company covered by the regulation fails to meet minimum cyber security requirements, fails to comply with instructions made under a national security power direction or recklessly or knowingly obstructs an investigation or inspection could face a far more impactful outcome.
Proposals include: a criminal penalty of up to $5 million or up to 2 percent of annual turnover for an entity and a criminal penalty up to $500,000 for a director. This would mark a major change in NZ's operating environment and align with the regulatory model of health and safety legislation.
Balancing outcomes for the greater good
Despite the headline numbers, it's evident that the New Zealand Government is concerned such mandates may prove negative for predominantly private sector owner operators.
Thresholds will be used to set out the definition of critical infrastructure and what organisations may soon be in scope - as such there is effort in the consultation's supporting documents to ensure not every business finds onerous requirements added to existing compliance activities.
"Imposing requirements on all electricity distribution networks could exacerbate energy poverty by imposing costs that would be recouped across a relatively small population."
Statements like this highlight the balancing act required to ensure that new security requirements dictated by future CNI regulations help ensure the continued provision of essential services whilst the changes to regulatory burden for critical infrastructure entities (and cost to Government to monitor and enforce) are not perceived as more than 'slightly negative' in nature.
Review the measures proposed for CNI operators in the full CNI consultation.
At Overcyte, as a local NZ provider to many CNI sectors, we'll be watching the progression of both the new cyber security strategy and action plan AND the proposed CNI regulations with a keen interest.







.png)

