Frameworks
"That's not a framework. THIS is a framework" Protecting Australia’s energy sector with the AESCSF

Successful attacks on Australia’s critical energy infrastructure could put essential services at risk.
The Australian Energy Sector Cyber Security Framework (AESCSF) is a voluntary framework and annual assessment programme for the country’s diverse energy sector.
It leverages international industry practices including the US Department of Energy’s Electricity Subsector Cybersecurity Capability Maturity Model (ES-C2M2) and the National Institute of Standards and Technology Cyber Security Framework (NISTCSF) amongst others.
The AESCSF also incorporates Australian-specific control references, such as the ACSC Essential 8 Strategies to Mitigate Cyber Security Incidents, the Australian Privacy Principles (APPs), and the Notifiable Data Breaches (NDB) scheme.
Developed through collaboration with industry and government stakeholders, the aim is to help energy market operators assess, benchmark, and improve their cybersecurity maturity in a coordinated and standardised way, strengthening resilience across a vital sector known to be under increasing attack globally.
CNI operators are actively targeted in Australia
A prolonged and widespread failure in Australia’s distributed energy sector could result in shortages of or disruption to essential medical supplies and food across the country, telecoms network outages and downstream disruption to transport and traffic management systems and critical fuel supplies for the country.
In the Australian Signals Directorate’s latest Annual Cyber Threat Report for 2023-2024, critical infrastructure made up 11% of all cyber security incidents with the electricity, gas, water and waste services comprising a third of those reports.
As an example of these attacks, the ASD highlighted how an energy supplier in New South Wales lost remote connectivity with the supervisory control and data acquisition (SCADA) system at two of its sites following a brute-force attack targeting a vulnerability in the company’s perimeter VPN devices.
Under a barrage of login attempts, MFA provided an effective control but even authorised connection requests were dropped. Whilst there was no interruption to energy supply in this incident, it took the company 8 hours to restore VPN services and highlighted the need to have effective security in place.
How and where the framework is applied
The first iteration of the AESCSF framework was released in 2018 and as Australia’s focus on regulating critical infrastructure organisations has grown, so too has the AESCSF.
In 2021 and 2022, the coverage was expanded to other Energy Market Operators including liquid fuels and gas markets and alignment sought with the Security of Critical Infrastructure Act (SOCI). Version 2 was launched in 2023:

The AESSCF is quite novel when compared with other international approaches – it comprises a set of security practices for Australia’s energy sector and a methodology for organisations to 1). assess their criticality within the national energy system and 2). their maturity against the security practices listed.
The Australian Energy Market Operator (AEMO) runs the national programme and states that the framework “describes what your organisation should strive to achieve, not how it should be achieved.”
The AESCSF is organised into 11 domains which group relevant practices together:
- Program (Cybersecurity program management)
- Workforce
- Cybersecurity Architecture
- Response, Continuity of Operations / Incident Response
- Third Parties / External Dependencies Management (i.e. supply chain etc.)
- Situational Awareness
- Threat & Vulnerability Management
- Identity & Access Management
- Asset, Change & Configuration Management
- Risk Management
- Australian Privacy Management (APM) which covers the handling of personal information.
Organisations initially use a Criticality Assessment Tool (CAT) to put them into a band (High / Medium / Low) based on how much impact a cyber incident could have on energy sector operations.
Ratings against the eleven practices are then made by selecting a Maturity Indicator Level (MIL) ranging from 1 to 3.
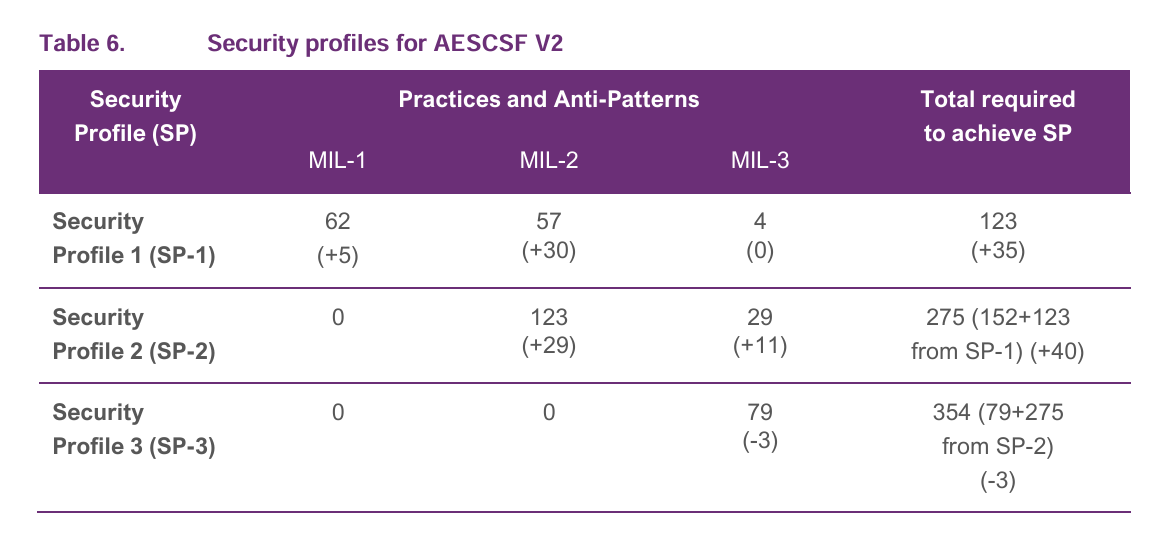
Security Profiles (SPs) are also set out for the set of practices – (SP-1, SP-2, SP-3) - which profile is applied is determined by the criticality rating. More critical organisations are expected to achieve more stringent cybersecurity maturity by aligning to a higher-level profile.
Anti Patterns that hinder cybersecurity maturity are also provided so that organisations can make efforts to avoid or mitigate them.
Sounds complex? Dig into the detail on the AEMO website to learn more.
Simplify your AESCSF assessment
Using Overcyte, companies can complete both parts of the AESCSF assessment:
- Criticality Assessment
- Cyber Security Capability and Maturity Self-Assessment
The platform enables the assessor to submit artefacts to support their ratings and score the practices one by one, adding findings and recommendations as they progress through the controls.

At SP-3, there are 354 Practices and Anti-Patterns across 11 domains and 37 subdomains.
A reporting dashboard provides an overall view of their maturity and areas to focus on in a future security uplift programme.

AEMO manages the formal industry programme of supervisory reporting which takes place each year. From February 2026, Australian energy organisations will be invited to participate in the new AESCSF Program and granted access to the portal. Benchmarking follows after the May deadline.
With Overcyte’s implementation of the AESSCF assessment, security teams can manage their ratings and remediation efforts in one single platform and have regular reporting to show progress before the 2026 round begins.
Reach out to us to learn more about Overcyte and how we can help.







.png)

