Australia
Strengthening critical infrastructure: Australia targets security uplift in areas of greatest risk

"as the threat environment continues to evolve and new technologies emerge, there is more we must do"
The Australian Government has kicked off consultations on urgent legislative reforms to further protect the country's critical infrastructure.
The Security of Critical Infrastructure Act 2018 (SOCI Act) is considered a 'world leading framework' that strengthens the government’s capacity to manage national security risks including espionage, sabotage and coercion arising from foreign involvement in Australia’s critical infrastructure.
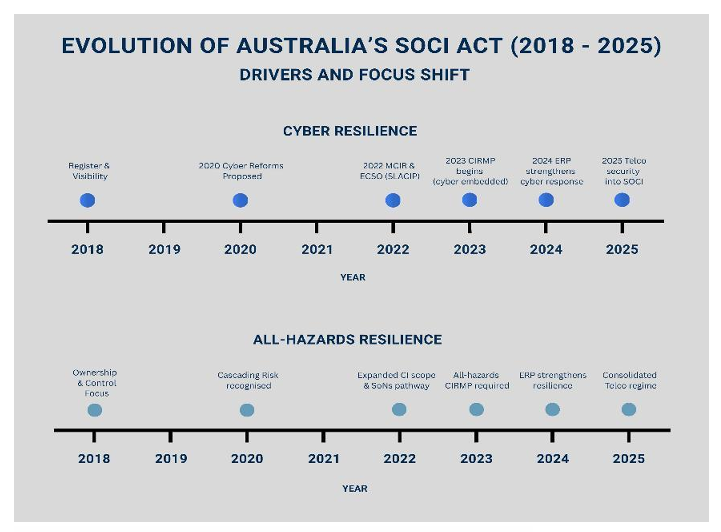
Since its commencement in 2018, the Act has undergone significant reforms, expanding coverage to additional sectors and introducing obligations such as mandatory cyber incident reporting.
Its aim is to ensure that asset owners and operators of critical infrastructure - often run by private sector entities - manage risks across all-hazards, including cyber and information security, physical, personnel and supply chain domains.
At the tail end of 2025, an Independent Review into the SOCI Act was undertaken by Dr Jill Slay AM to evaluate how the 11 sectors of critical infrastructure have responded to the security obligations over the last 7 years.
Testing the security waters
The Final Report - all 110 pages - was published just last month after 3 months of investigative work with covered entities. The overarching conclusion?
"the SOCI Act requires major legislative change to remove complexity and confusion while becoming more agile and responsive"
Overall, the consultation feedback was positive - Australia and Singapore maintain the most mature critical infrastructure frameworks globally - and seven years of mandated security measures had:
- Increased executive and board-level awareness of infrastructure vulnerabilities
- Established baseline governance frameworks and accountability structures
- Improved asset visibility and incident reporting mechanisms
- Created a common language for discussing critical infrastructure risks across sectors.
However, the SOCI Act was judged to not be equipped to handle emerging threats including AI and quantum risks and physical threat vectors such as drones and the dependencies on space based assets such as PNT systems.
Overall, a cyber-heavy focus neglected physical security, personnel security, and all-hazards supply chain resilience model.
The Space Industry Association of Australia (SIAA) noted that "space assets and space-related services are already fundamental to Australia's economy and society... yet are currently entirely outside of the SOCI framework."
Whilst Transport for New South Wales felt SOCI only partially achieved the intended outcomes and "duplication of state and federal obligations creates inefficiencies that detract from the Act’s effectiveness."
Consulting on critical infrastructure reforms
Post review, reducing complexity and improving the agility of the SOCI Act is now top of mind for the Australian Government. And thus, this week, public consultation on the first tranche of reforms has begun with:
- A consultation paper on proposed reforms to the Ministerial Directions power within the SOCI Act
- An exposure draft of the Enhanced Risk Management Program Rules
Consultation on Tranche 1 will run until 1 May 2026. Tranche two later this year will then seek to refine the SOCI Act and provide improved guidance.
Pimping CIRMP
The Critical Infrastructure Risk Management Program (CIRMP) is intended to uplift core security practices for the management of certain critical infrastructure assets.
Responsible entities of the asset classes listed in the SOCI Act Application Rules are required to establish, maintain, and comply with a written risk management program that manages the ‘material risk’ of a ‘hazard’ occurring.
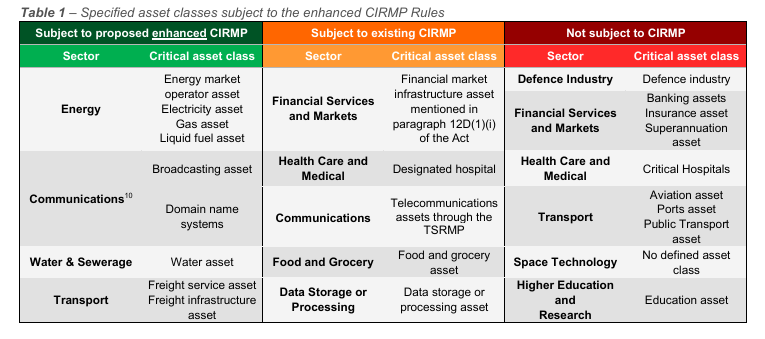
The new Exposure Draft introduces more prescriptive obligations for responsible entities of designated high-risk critical infrastructure assets, covering the energy, communications, water and sewerage, and transport sectors.
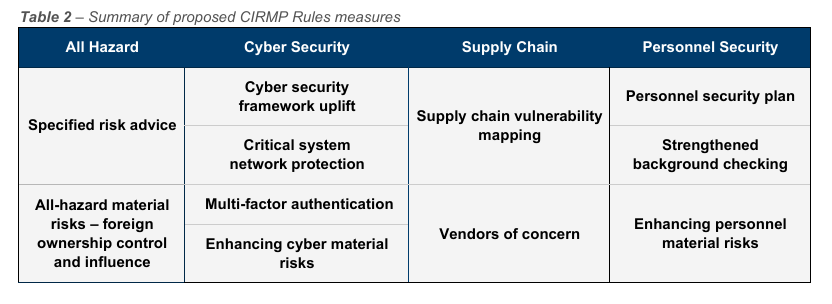
Items include:
- A mandatory uplift to Maturity Level 2 under a recognised framework (Essential Eight, ISO 27001, NIST CSF 2.0, C2M2 or AESCSF), implementation of phishing-resistant MFA, and network segregation ensuring critical systems can operate independently for at least three months.
- The mapping of major suppliers and critical systems, with vendor assessments addressing foreign ownership, control or influence (FOCI) risks and supplier access.
- Mandatory AusCheck background checks for critical workers and ongoing monitoring of personnel for insider threat.
- Management of physical security integrated with cyber, personnel and supply chain risk management - much like New Zealand's own Protective Security Requiremets framework for Government agencies.
Compliance with the new model will be required between 6 and 24 months after the changes come into effect.
Read more on the changes
- Consultation on proposed amendments to Ministerial Directions Powers and the Exposure Draft of the enhancements to the Critical Infrastructure Risk Management Program Rules under the SOCI Act
- Consultation on the Independent Review of the Security of Critical Infrastructure Act 2018
Given the scale of the proposed changes, the Department of Home Affairs is running two public virtual town halls during the consultation period to help parties digest key points.
There's also feedback to last year's CIRMP consultation worth reviewing, mainly from Australian energy sector suppliers.







.png)

